How to Apply the NIST Cybersecurity Framework in ICS | Industrial Defender OT/ICS Cybersecurity Blog

How to Apply the NIST Cybersecurity Framework in ICS | Industrial Defender OT/ICS Cybersecurity Blog

Amazon.fr - NIST Special Publication 800-82 Guide To Industrial Control Systems (ICS) Security - Nist - Livres

CPS architecture for an industrial control system testbed, following... | Download Scientific Diagram

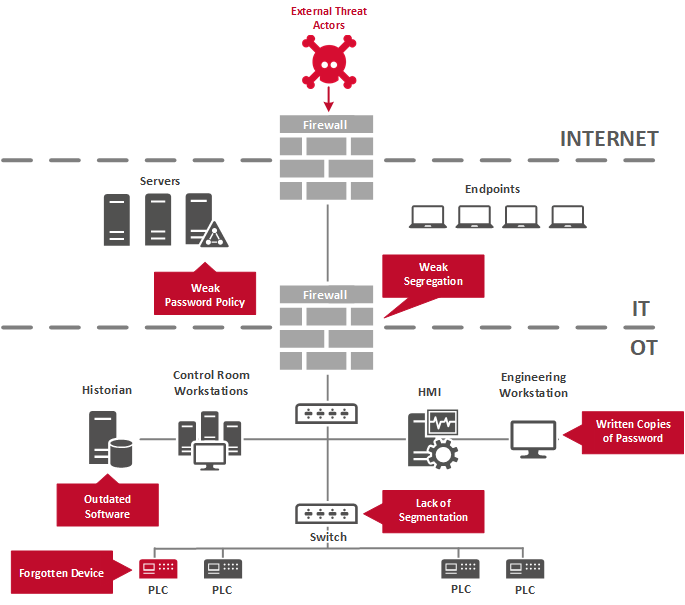
An Introduction to Industrial Control Systems Security Part II: An Overview of Protection Strategies | Cyber Security Leadership

NIST SP 800-82 Rev 2 - Guide to Industrial Control Systems (ICS) Security: SCADA and Other Control Systems : National Institute of Standards: Amazon.fr: Livres
![PDF] The NIST Process Control Security Requirements Forum (PCSRF) and the Future of Industrial Control System Security | Semantic Scholar PDF] The NIST Process Control Security Requirements Forum (PCSRF) and the Future of Industrial Control System Security | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e09da61b3badab0c1807d3d247e2728bfcb2e4a4/4-Figure1-1.png)