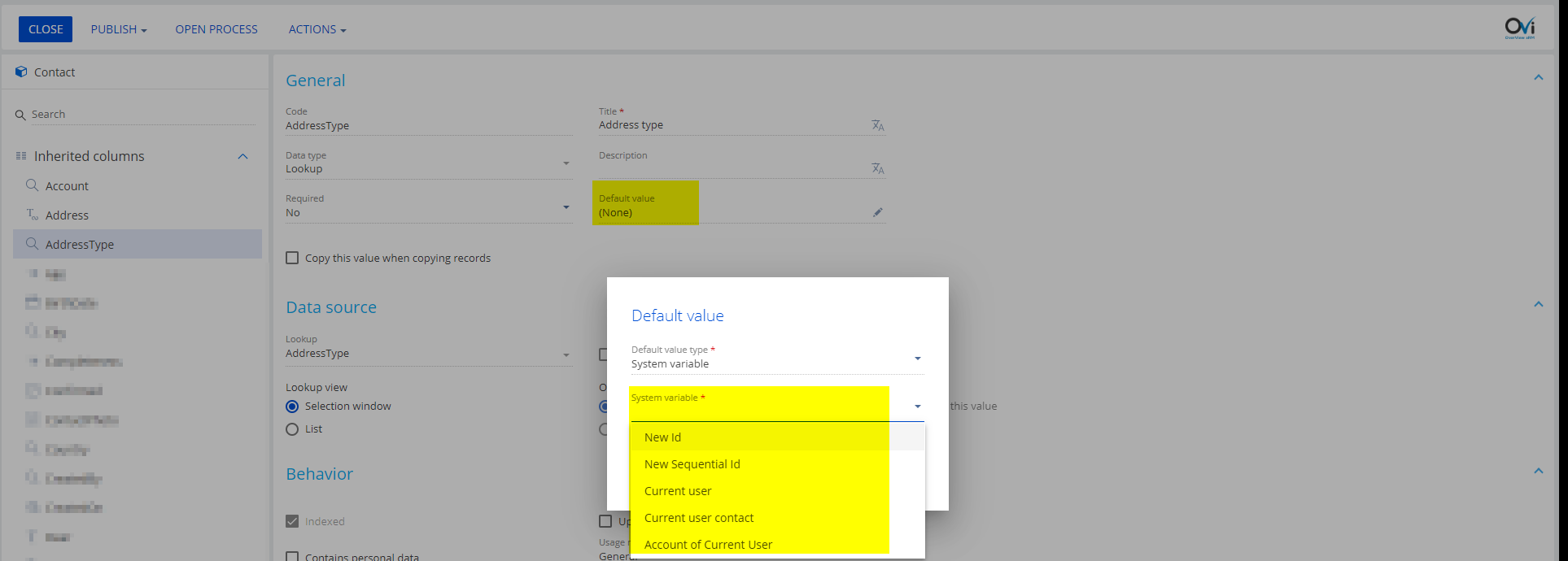
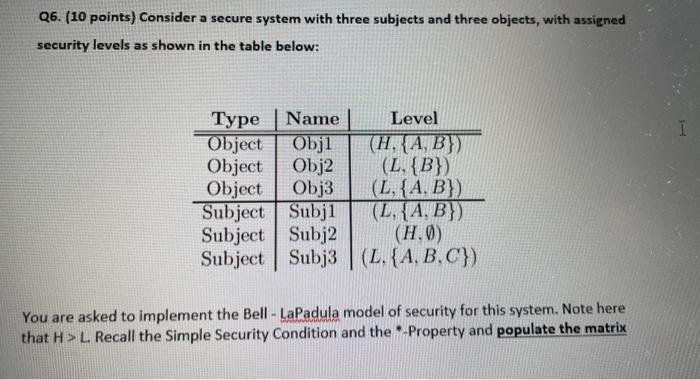
SOLVED: Suppose you have a secure system with two subjects and two objects, with levels as listed below. Type Name Level Object Obj1 (H,A) Object Obj2 (L,C) Subject Subj1 (L,B,C) Subject Subj2 (
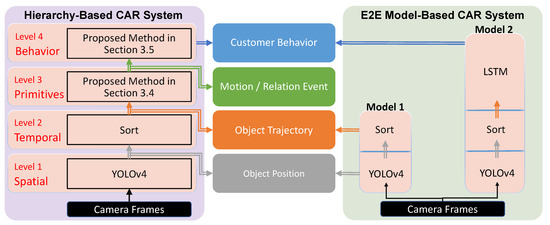
Sensors | Free Full-Text | A Hierarchy-Based System for Recognizing Customer Activity in Retail Environments

Electronic System Level Design: An Open-Source Approach: Rigo, Sandro, Azevedo, Rodolfo, Santos, Luiz: 9781402099397: Amazon.com: Books
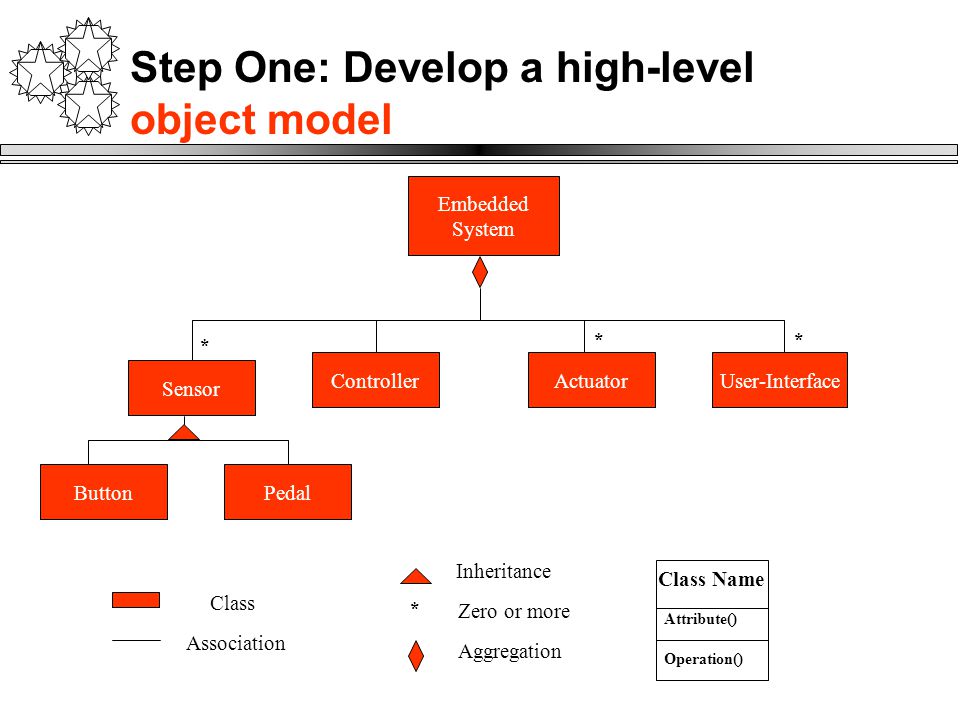
Embedded Systems Details. Object Model: Four main system objects or classes Controller object might be made up of several controllers is the brains of. - ppt download

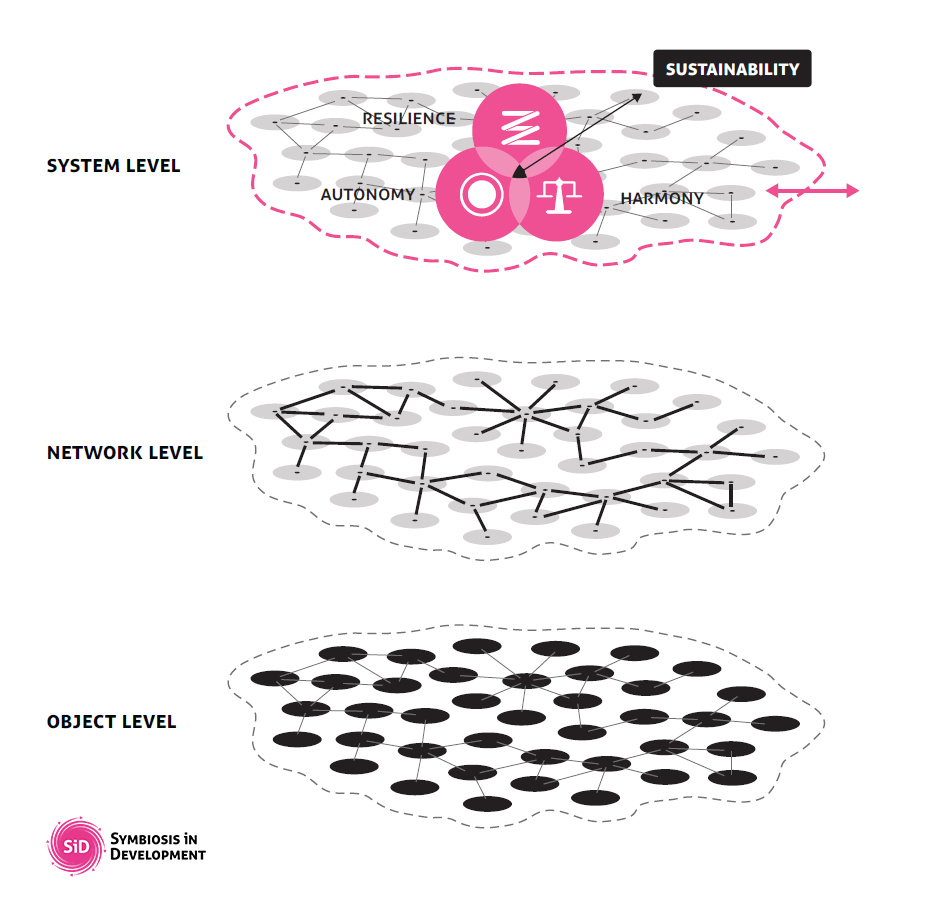
System-level architecture for building automation systems: Object-orientated design and simulation | Semantic Scholar












![PDF] An Object-Oriented Decision Support System: A Case of Inventory Management | Semantic Scholar PDF] An Object-Oriented Decision Support System: A Case of Inventory Management | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/71bad8aaa972f0d79fbc8664122eda507d6f6f5c/11-Figure2-1.png)